We find that while onboarding mechanisms exist in PWMs, they often play only supporting roles, and that the setup during initial PWM adoption still requires tedious manual work.
Our survey participants regarded PWMs as convenience tools, not security tools. We find that they are largely motivated by practical reasons and therefore mostly add passwords on the fly, while using a website, and that they prioritize which passwords they add to their PWMs at all. Additionally, distrust against malicious third parties or even the PWM vendors also plays an important role during strategy choice.
Publication #
Sabrina Amft, Sandra Höltervennhoff, Nicolas Huaman, Yasemin Acar and Sascha Fahl.
Nineteenth Symposium on Usable Privacy and Security (SOUPS'23), August 06-08, 2023.
Abstract
Password managers allow users to improve password security by handling large numbers of strong and unique passwords without the burden of memorizing them. While users are encouraged to add all credentials to their password manager and update weak credentials, this task can require significant effort and thus jeopardize security benefits if not completed thoroughly. However, user strategies to add credentials, related obstacles, and their security implications are not well understood.
To address this gap in security research, we performed a mixed-methods study, including expert reviews of 14 popular password managers and an online survey with 279 users of built-in and third-party password managers.
We extend previous work by examining the status quo of password manager setup features and investigating password manager users’ setup strategies. We confirm previous research and find that many participants utilize password managers for convenience, not as a security tool. They most commonly add credentials whenever a website is visited, and prioritize what they add. Similarly, passwords are often only updated when they are considered insecure. Additionally, we observe a severe distrust towards password managers, leading to users not adding important passwords.
We conclude our work by giving recommendations for password manager developers to help users overcome the obstacles we identified.
Replication Artifacts #
In line with the effort to support replication of our work and help other researchers build upon it, we provide a replication package and an artifact repository.
| Filename | Type |
|---|---|
| expert-review.txt | List of tasks for the expert reviews |
| Expert Review Videos | Screencasts made within our expert review |
| survey-questions.txt | Questions for both the pre-survey and our full survey |
| code-book.csv | Codebook for survey coding |
| supplementary-texts.txt | Job Descriptions & Consent form |
| Additional Material | Folder with additional graphics detailing our survey results (will be added soon) |
Paper Overview #
We conduct 14 expert reviews of popular PWM extensions to create an overview of current onboarding and adoption features. Following this, we survey 279 end users about their initial PWM adoption experience, which strategies they used to include passwords, and their habits and sentiments regarding the setup process.
- We find that while PWMs already include some features to ease the initial setup, they are mostly focused on imports, auto-saves and tutorials. Many security-focused features such as breach warnings are only available for premium plans.
- Many participants utilize password managers for convenience, not as a security tool. We additionally observe a severe distrust towards PWMs.
- Participants most commonly add credentials whenever a website is visited, and prioritize what they add. Similarly, passwords are often only updated when they are considered insecure.
Overall, we give several recommendations for additional or improved features within PWMs, to smooth the existing processes for PWM adoption, and easing users into the tedious task of adding their passwords. Our aim is to increase security by removing the obstacles that users face when trying to fully benefit from PWMs.
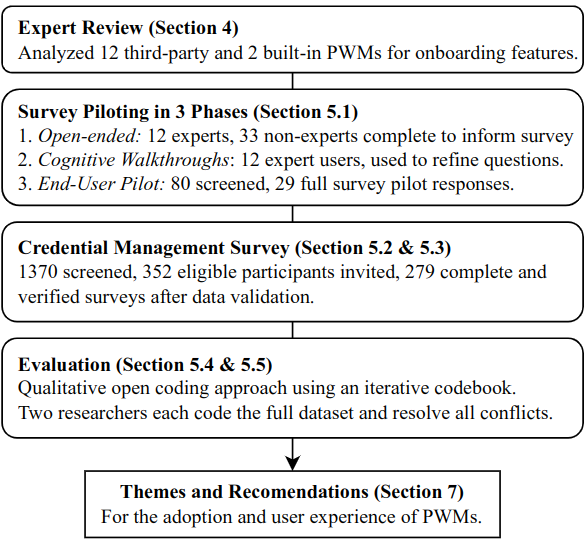
Figure 1: Overview of our methodology: Our expert reviews are followed by a survey with 279 end users.
Motivation #
Despite investigations into new online authentication standards, usernames and passwords remain the most widely used. Users need to manage an enormous amount of online credentials, which has only increased with the growth of online communication during the recent global pandemic. Due to the number of accounts, users face an immense cognitive burden when creating and memorizing strong and unique passwords for all of them.
A promising way to mitigate the above challenges is the use of password managers (PWMs). They allow users to maintain all their passwords and often additional information such as credit card data, addresses, or two-factor authentication secrets behind a single master password. Users therefore only need to memorize this one password, removing most of the cognitive load. Most PWMs furthermore provide password security checks, the generation of strong passwords, and provide auto-save and autofill features.
However, the initial PWM setup requires a lot of time and effort: Users need to choose and install a PWM as well as potential web browser extensions, gather their online accounts, add them one by one into the PWM and ideally also update weak, re-used or leaked passwords. All of this is time-consuming and requires users to have a list of all of their accounts ready if they want to set up their PWM as quickly as possible, but composing this list is often a challenging task. On the other hand, the effective security benefits of PWM are reduced if users do not add and upgrade their credentials when adopting the PWM, as passwords might remain reused or easily guessable.
Expert Reviews #
We were interested in features that can support users with the tedious initial setup processes when adopting a PWM, i. e., features that were designed to help them add passwords and replace them with strong alternatives where necessary to increase the security benefits from using a PWM. We used the expert reviews findings to inform our survey and design recommendations for PWM developers.
Two authors conducted expert reviews of the 14 most popular PWMs, including both offline PWMs and online PWMs with cloud storage back-ends, as well as the PWMs built into Chrome and Firefox. We performed a set of tasks users typically encounter after setting up a PWM, and aimed to include both common tasks, and workflows that increased security by, e. g., upgrading password strength.
Findings #
We identified three different categories of features that help users when initially adding their credentials:
1) User Motivation and Education. #
This type of feature serves as a first introduction to the PWM. We found tutorials present in half of all reviewed PWMs, while next step lists were offered in four. With LastPass, we additionally found one PWM that coupled its guides to achievements or badges to incentivize their completion and motivate users to get acquainted with the most important features.
2) Ease of Password Storage. #
We found different functionalities aiming to ease the process. Most importantly, almost all tested PWMs except the Firefox built-in offered some kind of bulk import from other PWMs, browsers, or raw .csv files. However, we found the expected import formats to differ widely, and we found different requirements for .csv files in terms of, e. g., required columns and data formatting.
A slower approach is the ability to auto-save passwords while browsing, in which the PWM extension offers to store credentials whenever the user logs into a website or registers new accounts. We found this available in almost all PWMs, however, it was only available as a premium feature in one.
Finally, we found four PWMs that suggested popular websites when adding new accounts, which is useful to help users remember which accounts they might have.
3) Secure Passwords. #
While password meters are the best-known features to help users create strong passwords, we only found them in seven PWMs. When included, we often perceived them as counterintuitive.
Other measures include security centers, i. e., dashboards in which users receive comprehensive summaries of insufficient credentials that are, e. g., weak, reused over multiple stored entries, generally common, or present in leaks. This was present in a majority (ten) of evaluated PWMs. However, we found it often only available in premium account plans
A similar feature, often included within security centers, are breach reports, in which either the user’s email address or the passwords within the PWM are scanned for their presence in credential leaks. While present in almost all PWMs, breach reports are typically a premium feature that is not accessible for non-paying customers.
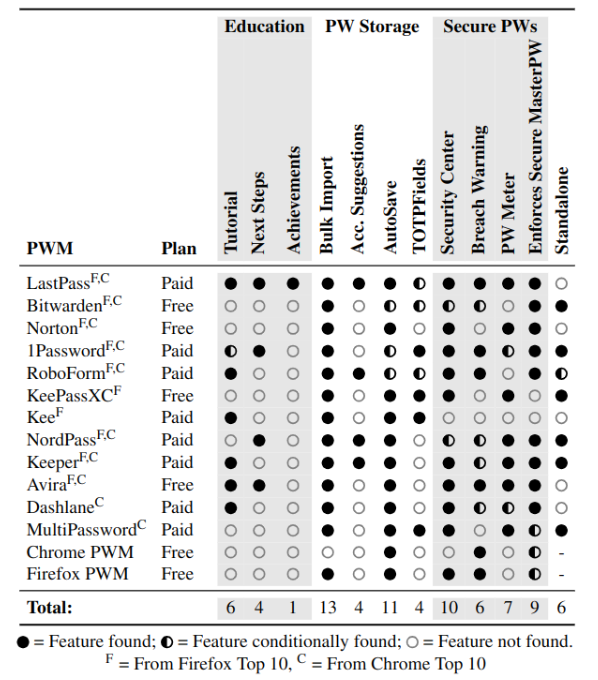
Figure 2: Overview of on-boarding features present in popular PWMs. The browser columns indicate that the respective PWM is present in the top 10 PWMs at the time of our analysis.
Survey #
We designed the survey to explore which credential management strategies users apply when they initially set up their PWM, i. e., how they add their passwords, and in which ways they interact with their PWM to increase task efficiency or password security.
We first included PWM demographics regarding their PWM choice and usage. Overall, we aimed to investigate the spread of the PWM credential management strategies we identified, as well as what influenced a users’ decision to apply a strategy. Therefore, we asked participants about the strategy they mainly applied both in an open-ended question to gather unbiased experiences and sentiments, and a closed-ended version on the next survey page to better pinpoint the precise strategy. We further asked participants to describe reasons and alterations for their strategy, and their current strategy to account for changes over time.
Furthermore, we were interested in how participants dealt with their existing passwords - i. e., whether they changed all, some or none of them when they set up the PWM, their password generation process and their experiences with the setup process.
To further collect insights into problems and usability improvements, we directly asked participants what their PWM could have done to improve their personal setup process. Finally, the last part of our survey covered common demographic questions.
Survey Results #
Overall, we found that most participants add credentials whenever they access the respective services. This was often motivated by efficiency, convenience, or a lack of overview over their online accounts. Due to this, security was only a secondary factor, and many participants were deterred from investing time and effort to improve their online credential security.
We identified seven main strategies. We mainly distinguish them by the time passwords were added (e. g., immediately on install, or when services are accessed) or the choice of which passwords were added (e. g., for more or less important or frequently used accounts).
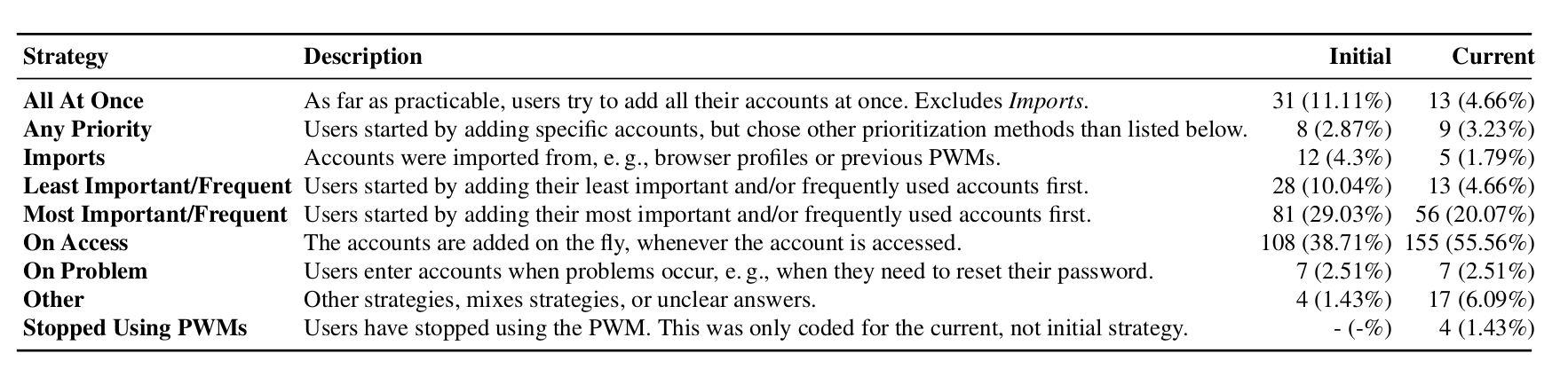
Figure 3: Participants’ strategies to insert credentials into their PWM
Credential Management Strategies. The most frequent initial strategy was to add accounts whenever they were accessed for the first time after the PWM setup (108, 38.71%). This often uses auto-save features, i. e., the user does not necessarily need to consciously or manually add passwords, but can simply follow a prompt. Following, users reported to have added their most important or frequently used accounts first (81, 29.03%). This was most often reported as an attempt to save time, since adding all accounts was time-consuming. We found all other strategies to be less relevant in practice. From a security perspective, adding and updating all passwords at once would be ideal. However, we found only 31 (11.11%) participants to specify that their strategy was to add everything at once. We found that 28 (10.04%) users mentioned adding their least important or only rarely used accounts, often referring to security concerns or simply wanting to test the PWM before adding relevant accounts as reasons:
“I started with the less important accounts because I wanted to get used to the tool before importing my important account information.” (P14)
In addition to their initial strategy, we asked participants to provide their current one, and to detail potential changes and reasons. We found a huge increase in users who add their credentials on access (155, 55.56%). As we were asking for the current strategy, this relates mostly to accounts that users freshly create, and that the majority of users immediately add to their PWM, presumably with the help of auto-save features. Again, the second-largest group of participants reported prioritizing important or frequently used accounts (56, 20.07%), suggesting that in these cases, lesser important accounts are never added. We found other previously mentioned strategies mostly irrelevant after the initial setup.
Most participants chose their initial strategy due to its efficiency (113, 40.5%) or because it was perceived as the easiest approach (94, 33.69%). We found all other reasons less common, such as security increases (46, 16.49%), wanting to add or exclude specific accounts (43, 15.41%), or having problems remembering all accounts or passwords or not wanting to remember them (37, 13.26%). When regarding specific strategies, we found that imports were more often described as convenient, and that adding all accounts at once was more often done out of completion, but less often out of convenience or efficiency.
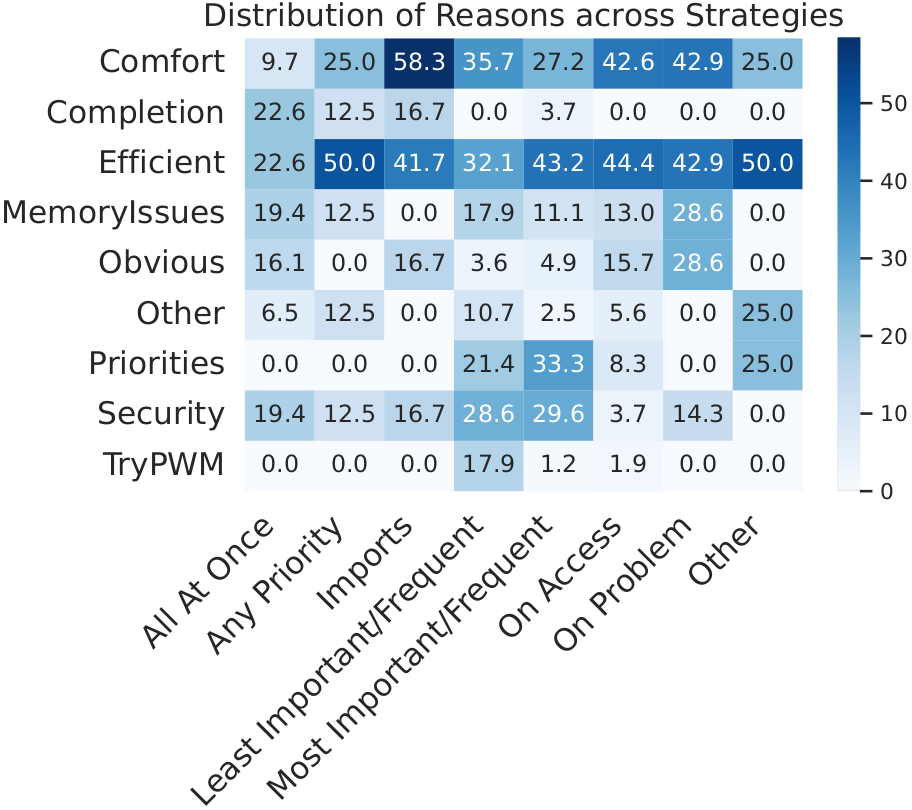
Figure 3: Distribution of reasons for different strategies applied by our participants in %.
Finally, we used participant answers to investigate whether they utilized the best-case strategy for security and not only added all of their accounts, but also updated every password to a stronger alternative. We found that almost no participants (14, 5.02%) used this approach. Participants mainly argued that adding everything would have been too much work (97, 36.6%), but also that they did not trust their PWM enough to add all important passwords (42, 15.85%).
We also found participants who stated to be unable to recollect all their accounts (40, 15.09%), as one participant explains:
“I can’t even remember that they exist, I can’t just suddenly remember all of them and add them to the manager.” (P142)
General PWM Usage. We found that half of the participants stated to store all their private passwords, and an even higher portion that indicated to store every work-related password (65.59%). For those who do not store all private passwords, common reasons included distrust towards the PWM (78, 52.7%) as well as prioritization which passwords should be added (68, 45.95%). We assume that participants are more likely to store all work passwords because they have a lower, more manageable amount that they on average use more frequently.
When asked which website types they prioritized to add, users most commonly mentioned Social Media (78, 27.96%), followed by finance-related websites (47, 16.85%) and email credentials (44, 15.77%).
Since the opportunity to upgrade passwords is an important part of PWM usage, we wanted to know if users did this when they added credentials. Most frequently, they state to have changed some passwords (116, 41.58%), with only 59 (21.15%) who upgraded all of them, and 53 (19.0%) who kept all passwords. We found that reasons to change the passwords were mostly focused around general security increases (35, 22.29%), or to improve weak (55, 35.03%), reused (31, 19.75%) or leaked (14, 8.92%) passwords. Users who decided to keep their old passwords mentioned that their passwords were already strong enough (24, 28.92%), or, a lack of motivation and simply having no reason (26, 31.33%).
“And it is not enough to generate a password in the application, you also have to identify yourself on the website, change the password, verify the change… Would you give the same priority to the bank and a game page? Because I do not.” - P117
Comparing Built-in and Third-party PWMs. As we surveyed both users of built-in and third-party PWMs, we were interested in differences and similarities.
Third-party users tended to add accounts more often based on their relevance or to add everything at once initially, although we found no difference within the current strategies, likely because users now have added all existing accounts, and strategies have shifted towards only adding new accounts on access.
While built-in users were more often driven by comfort and efficiency, third-party users chose their strategy based on security concerns, and to make sure that either all accounts, or specific important ones were included within their PWM. Similar to this, we found built-in users more likely to worry about issues such as an overwhelming amount of accounts or forgetting their passwords.
However, third-party users were more interested in increasing their overall security, enjoyed the reduced cognitive load of having to memorize only one master password, and were curious to test the PWM, which makes sense as third-party tools require a conscious choice and installation.
Recommendations #
Automation
- Ease processes by using overall more automation.
- Use novel approaches such as well-known URLs within websites to enable auto-updates.
- Implement standardized format for database exports and imports.
Account Scans
- Scan, e.g., email inboxes or browser histories to collect account lists or suggest accounts to add.
- Utilize optic character recognition to scan handwritten password notes and import them.
Account Suggestions
- Suggest users common accounts or popular websites they might still need to add to their PWM.
- Similarly: Suggest deletion of older, incomplete or unused accounts.
Guided Additions
- Implement internal tables to compile and edit account lists, instead of solely relying on imports.
- Allow bulk edits.
- Guide users better through the process.
Privacy Labels
- Adopt privacy labels to mitigate distrust due to lack of knowledge or familiarity. This can help non-experts to quickly assess the security and risks associated with using PWMs.
Gamification & Nudges
- Evaluate achievements and other gamification measures to make tedious tasks more enjoyable.
- Add nudges to remind and motivate users to store or update passwords.
Acknowledgements #
We thank all participants for their valuable time and insights shared with us. Funded by the Deutsche Forschungsgemeinschaft (DFG, German Research Foundation) under Germany´s Excellence Strategy - EXC 2092 CASA – 390781972.
Cite This Work #
@inproceedings{conf-soups-amft23,
title = {“Would You Give the Same Priority to the Bank and a Game? I Do Not!” Exploring Credential Management Strategies and Obstacles during Password Manager Setup},
author = {Sabrina Amft and
Sandra Höltervennhoff and
Nicolas Huaman and
Yasemin Acar and
Sascha Fahl},
booktitle = {Nineteenth Symposium on Usable Privacy and Security},
month = august,
year = {2023},
url = {https://www.usenix.org/conference/soups2023}
}Amft et al. "“Would You Give the Same Priority to the Bank and a Game? I Do Not!” Exploring Credential Management Strategies and Obstacles during Password Manager Setup." Nineteenth Symposium on Usable Privacy and Security. 2023. Amft, S., Höltervennhoff, S., Huaman, N., Acar, Y., & Fahl, S. (2023, Augst). “Would You Give the Same Priority to the Bank and a Game? I Do Not!” Exploring Credential Management Strategies and Obstacles during Password Manager Setup. Nineteenth Symposium on Usable Privacy and Security (SOUPS'23).%0 Conference Proceedings
%T “Would You Give the Same Priority to the Bank and a Game? I Do Not!” Exploring Credential Management Strategies and Obstacles during Password Manager Setup
%A Amft, Sabrina
%A Höltervennhoff, Sandra
%A Huaman, Nicolas
%A Acar, Yasemin
%A Fahl, Sascha
%B Nineteenth Symposium on Usable Privacy and Security
%D 2023TY - CONF
T1 - “Would You Give the Same Priority to the Bank and a Game? I Do Not!” Exploring Credential Management Strategies and Obstacles during Password Manager Setup
A1 - Amft, Sabrina
A1 - Höltervennhoff, Sandra
A1 - Huaman, Nicolas
A1 - Acar, Yasemin
A1 - Fahl, Sascha
JO - Nineteenth Symposium on Usable Privacy and Security
Y1 - 2023
ER -
